- 106 Posts
- 3.01K Comments
Lol, no. Most of maga can’t even spell Europe, so all of those things you list, while true, are way beyond their comprehension.
The politicians just point at European countries and say they stupid because they talk funny and they are stealing from you. (It doesn’t matter if that is true or not, it’s just “someone else to blame” for made up problems.)

 8·3 days ago
8·3 days agoAlumina (aluminum oxide) is what you are extracting from aluminum ore and it’s tough as fuck, which is why it’s easier to dissolve the rest of the stuff around it first.
Oxygen is mainly that other “junk” you have to separate with electricity. While the smelters only run at 4.5 volts (per cell), they have to push about 300kA to get the stuff up to ~950°C which breaks its chemical bond.
You probably have never even touched pure aluminum before. Aluminum and oxygen react so quick, all we typically ever see and touch is a alumina shell.
LEGAL LOGIC TWIST EVERY GUESS FINAL

 31·4 days ago
31·4 days agoI am not sure if I would trust a company that claims a glorified fanny pack will protect your health from EMF radiation.

 3·5 days ago
3·5 days agoLike others have said, take a break from the internet for a while. (After this particular post slows down and you digest what people here have to say, of course.)
On Lemmy, my habit is usually to block every controversial community that I can. If I see trolls that hang out in specific communities, I’ll usually block them before they get a chance to interact with me. My feed here is fairly clean, but it took a while to filter out the dozens of political communities. (Political communities are breeding grounds for controversy, so stay away from the comments if you can.)
If you game, stay away from any toxic gaming communities or disable all chat if you can.
You may feel like you are missing out on things the more you sanitize your interactions online. Don’t worry, you aren’t.
Its harder to filter for people who may randomly attack you online. Self-control is paramount: The second you read a word of something negative, stop reading that comment and block that person if possible.
Still though, blocking and filtering only goes so far. The internets can be a hostile place whatever forum you are on. When you are able, it just takes a ton of patience and practice to properly ignore what you read online.

 11·5 days ago
11·5 days ago$50 Canadian for 6 packs at Costco.
That is an expensive bag of fiber.

 3·5 days ago
3·5 days agoI don’t think it matters much if ee is shutting down.

 152·5 days ago
152·5 days agoReading the first 3 words of the title as English was disturbing.

 2·8 days ago
2·8 days agoThat is not really a contradiction and again, let’s put rights and freedoms in grammatical context using this example: “Freedom of speech is a right.” Think about that for a second if you need.
I live in Colorado which is subjectively the weed capitol of the US. Even so, it is illegal to smoke in public places unless it’s a designated event which is usually on private property.
Weed is an intoxicating drug. As such, it’s customary to restrict the consumption of intoxicants in public. (Hence, it’s a law. There is more to this, but out of scope of this conversation.) In theory, the consumption of weed is reduced downtown because people don’t want to get a fine or a ticket.
It’s a personal freedom to light up wherever the hell you want. If I say, out loud, that I am going to go downtown and smoke a fatty, nobody can throw me in jail for that or tie me up because I said something. If I actually do go downtown and light up, that is not within my legal rights and that action may have consequences.
It’s my right, as defined by law, not to smell it in a zone that is designated as weed-free, and notify the police. The police, should protect my rights in that case. (In theory.)
Your freedom to smoke-up was not restricted and my legal rights are enforced by the police.
In the interest of this conversation, I am using “context” is very broady. It may include: Local and state laws, criminal history, reputational history, being on public or private property, current behavior, state of intoxication, and literally the thousands of other in things that lead-up to or describe a scenario.
Legal freedoms and legal rights have limits and those limits are contextual. If I disagree with any legal right OR legal restriction, I can get an attorney and attempt to change a law and petition my government. Those are also my rights.
What is absolutely important is understanding how your rights and freedoms are defined by law. Arbitrarily saying things like, “I have the right to smoke where I want” doesn’t cut it.
Again, the only freedoms and rights you have must be defined by law. Those freedoms and rights are not limitless BUT are subject to legal interpretation in their appropriate context AND you have the legal means to adjust that interpretation.
Edit: I am using words here with purpose, so try not to skip over bits. It is extremely challenging to discuss complex topics on social media and I am attempting to be as neutral and unbiased as possible. Separating “rights and freedoms” from “legal rights and freedoms”, with all nuances attached, is always a rough topic, btw.
Edit2: Changed typo: “non limitless” to “not limitless”.

 8·8 days ago
8·8 days agoShifting the word from “freedom” to “rights” makes more sense in the context you are explaining. (There isn’t that much of a difference, but “freedom” implies a choice without restriction where as a “right” may have implied boundaries.)
Every situation you described can be boiled down to a single question: Do my actions impact or otherwise restrict the rights of others? (That is the guideline, btw.)
Rights are contextual and may have different legal definitions depending on where you live or where you are.
Most importantly, unless you are imprisoned or physically restrained, you have the freedom to do whatever the fuck you want. However, that doesn’t mean your actions are within your rights and those actions could have serious consequences.
It’s just a bit of wood attached to a fairly big chunk of explosive and I would guess that wood shrapnel is just as deadly as metal within its effective range. The stick isn’t going to block much of anything.
Stick grenades could have a fragmentation sleeve, but they relied more on the explosive concussion for damage, not the shrapnel.
when u really smell weed coming from ur neighbor’s backyard…

Gravity is not a constant and that would probably matter at the precision that needs to be measured in the given test environment. In any other situation, gravity (or the state of the earths magnetic field) would generally not matter enough to measure.
The precision of F=MA might even be debatable as an accurate formula at these scales… I dunno about that though.
https://en.m.wikipedia.org/wiki/Gravity_of_Earth
https://earthobservatory.nasa.gov/images/84266/measuring-earths-magnetism

 51·12 days ago
51·12 days agoI agree, it seems that you have enough room for the length of the card.
For compute-only GPUs, you just plug them in any way you can if your power supply has enough wattage to support it. You can even get 16x to 1x pcie slot adapters for just that purpose. 16x vs 1x basically means slot length, in our context. (It’s commonly done for Bitcoin mining.) Compute is different as it generally doesn’t have the low latency requirements that a game would. PCIe is very robust when it comes to backward compatibility.
When it comes to running and AMD card and NVIDIA card together, I know windows handles it OK. I am not sure about Linux compatibility or what issues you may see.
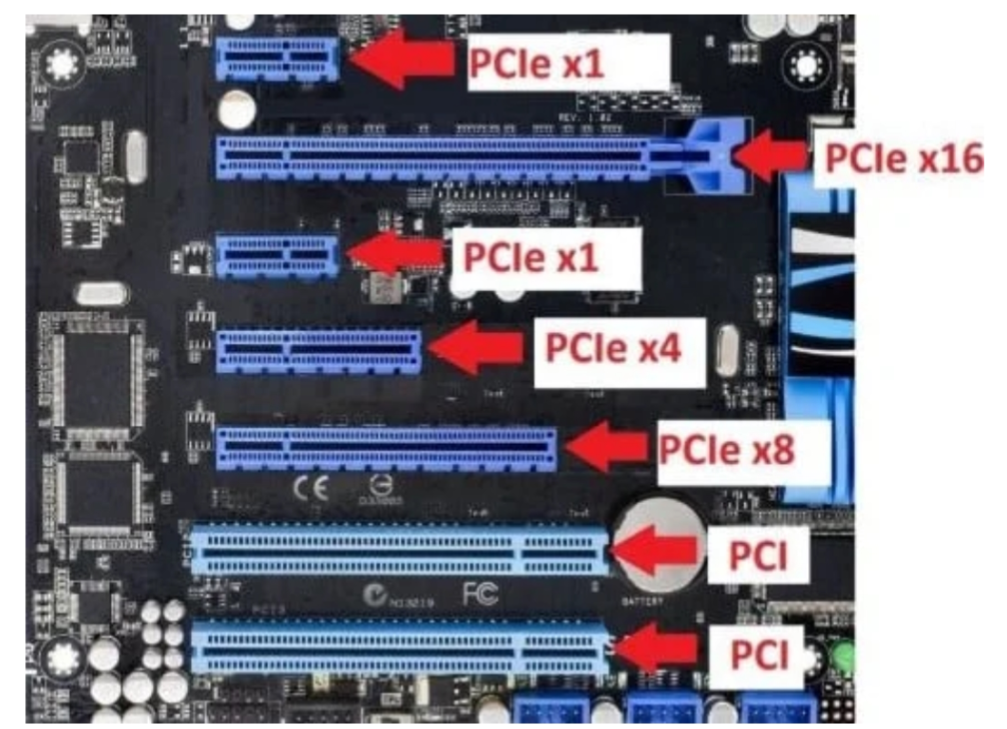

 5·12 days ago
5·12 days agoOk, I wasn’t expecting a server-class card but it should be fine without its support bracket. Generic cases generally wouldn’t have a place to connect the support to. (Some might, but I can’t see the rest of the case. Your picture doesn’t actually show how much space you have to insert a longer card.)
The dimensions of the P100 is 10.5 inches in length and 4.4 inches in height, so you should be able to measure for clearance. My 7900 XTX is 11.3in, and it will fit in many towers so I have confidence that the P100 will fit in yours.
Still, It’s a long card so you might want to look around for a generic GPU support bracket to keep it from sagging over the long-term.
DIMMs (dual inline memory modules) are your ram sticks, yes. Typically, they run in pairs for best performance. So, generally, you would populate slot B and slot D for the first pair and slot A and C for the second pair. Regardless, the PC will generally still run with mismatched pairs, but it will clock itself down to the speed of the slowest module installed and may run in single-channel mode. This, in turn, slows the performance of the entire PC down by creating a bottleneck on the memory bus.
Edit: I haven’t thought about slot height in a while, but standard cases are going to be full-height cards. Half-height cards are more niche.

 6·12 days ago
6·12 days agoWhat video card are you getting? You are probably thinking single or double slot thickness cards. Your old card is double slot.
Also, is that just 3 DIMMS? Check the manual for specifics, but an unmatched pair could be tanking your memory speed worse than just having less memory.





















https://lailluminator.com/2025/05/19/weather-modification-bills/
These bills are fueled by conspiracy theories and idiocy.